Master Real-World Tactics, Not Just Theory
The COSP program bridges the gap between basic knowledge and the expert-level skills employers demand. In our 70% hands-on virtual labs, you will learn by doing—mastering everything from advanced network pivoting and Active Directory attacks to modern API hacking
Your direct path to a high-stakes cybersecurity career

Transform Your Cybersecurity Skills
Step into a world of cybersecurity challenges with hands-on training and simulations.

Become the Professional Attacker's Fear
The industry is desperately seeking experts who can think like an attacker to defend critical assets. The Training program is your direct path to these lucrative roles, transforming you from a novice into a certified professional with proven, in-demand offensive security skills.
Go beyond basic knowledge. Achieve expert-level skill.
Enter The Cyber Range
This is where theory ends. In our 70% hands-on virtual labs, you will learn by breaking into realistic systems, mastering the tools and offensive tactics used by top penetration testers in the industry.
Hack the way outTraining & Internship
No matter your background, with a growing library of courses and simulations, there are no limits to your cybersecurity knowledge and skills.
Enroll in Internship Program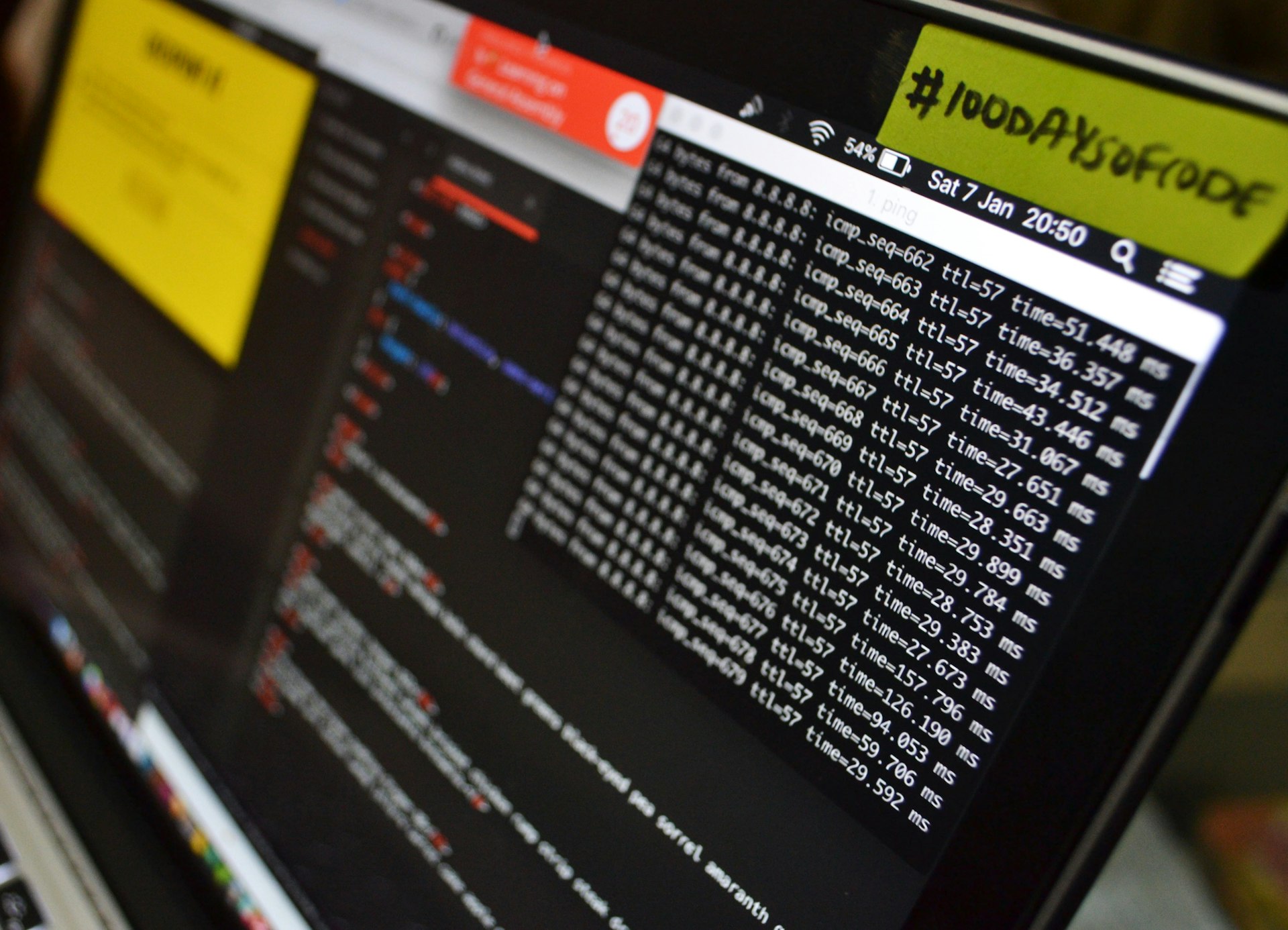
Security & Assurance
We prioritize high-quality content and resources. Our training materials are regularly updated to reflect the latest cybersecurity trends and best practices. All our programs come with a satisfaction guarantee.
Discover more
Engaging content
We prioritize high-quality content and resources. Our training materials are regularly updated to reflect the latest cybersecurity trends and best practices. All our programs come with a satisfaction guarantee.

IOTs Hacking Essentials
Hacking via IoT (Internet of Things) is the exploitation of everyday smart devices. Attackers easily gain control through vulnerabilities like default passwords and a lack of security updates. They then force these compromised devices into massive botnets for DDoS attacks, spy on users, or infiltrate secure networks.
Learn More